Sneaking into Black Hat
With DEFCON qualifiers coming up again, I (cts) thought I’d share me and Jazzy’s experience at Las Vegas last year.
Though we missed qualifying for DEFCON finals (by 1 place!), we were nevertheless generously invited by Hackerone to their h1-702 event, and luckily for us Black Hat 2018 and DEFCON happened to coincide!
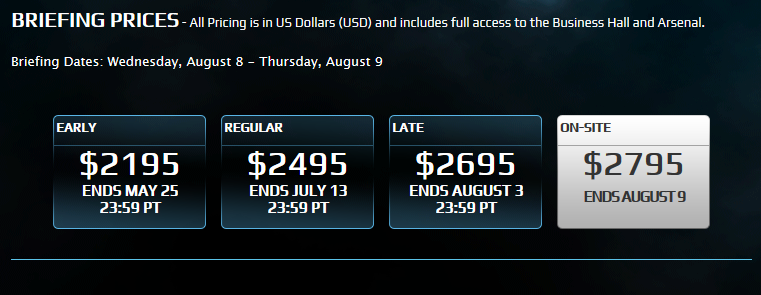
Now…everyone knows DEFCON is a scam, but at least tickets are affordable. Black Hat tickets are $2000 and up (!!!!), not in the range of students like us.
It was Day 0 of Black Hat, and we had no badge. So what did we do? As it turned out, we had a friend at h1-702 who was willing to lend us his legitimate badge. He himself was lucky enough to have a student pass. Being the creative hAcKeRs we were, we made use of the limited resources we had available to us at the Aria.
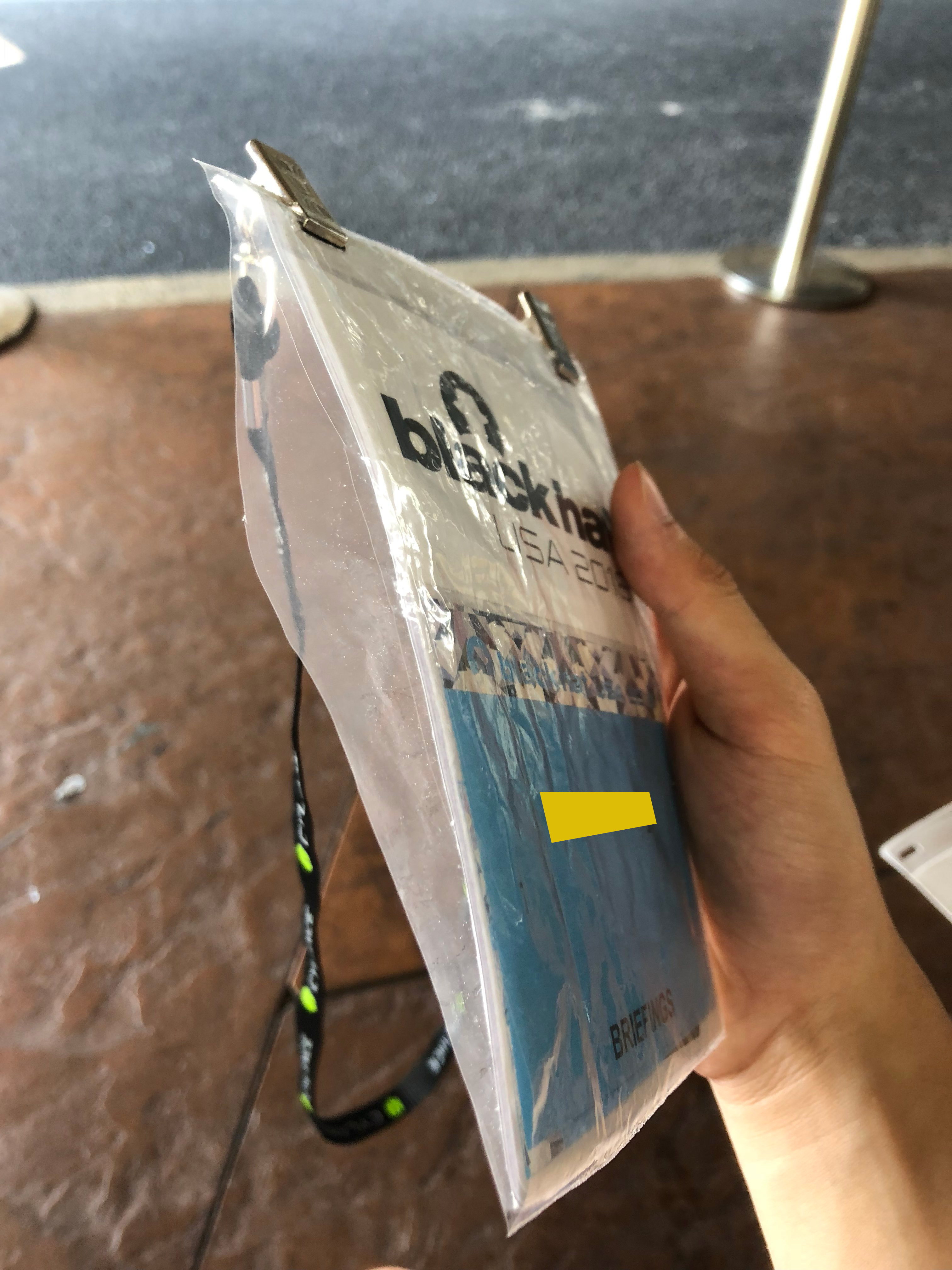
- 1 (one) ziploc bag, originally filled with protein powder
- 1 (one) pair of scissors borrowed from Kevin at the Aria Business Center
- 1 (one) valid badge
- 1 (one) roll of Scotch tape
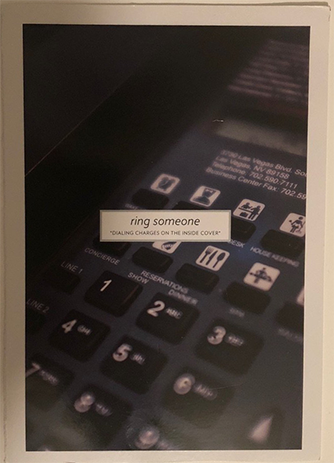
- 1 (one) random piece of card paper from the hotel room
First, we took the real badge and photocopied it at the Business Center.
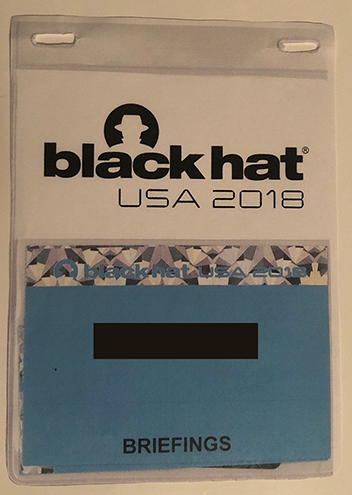
Next, we cut out the badge from the photocopy and also cut holes for the lanyard as in the real badge. We then trimmed the zipper off the ziploc bag and arranged the buffet. The card paper was a backbone for structural support: it afforded some thickness to the flimsy photocopy.
But now we had a problem! We had two badges (one real, one fake), but only one lanyard! To circumvent this, Jazzy simply took his badge to Registration, claiming he’d “lost” his lanyard. Once they’d replaced it, we now had two lanyards and two badges.

Looks pretty good, eh? I also kept a business card on hand to just in case anyone questioned my identity.
This was more than enough to get into the conference, but getting into the keynote on Day 0 proved to be more challenging. At the door, they were checking the RFID cards in the badge. We had the equipment on hand to clone RFIDs (reader, writer); however, we didn’t have an Arduino to drive them. Instead, we opted to sneak in using a Layer 0 backdoor.

And that’s how we snuck on Day 0 at Black Hat 2018!. There wasn’t much going on, so we were in and out in 15 minutes On the next day, we finally had our student badges ready, so we were able to attend the talks unimpeded. There’s so much that I left out here that I didn’t get to cover, such as the great time we had at h1-702. But that’s a story for another time… :) That’s all folks.
